VPN Configuration
Most tech savvy businesses are investing in VPN not only for the purpose of having fast, scalable and resilient networks, but also because it provides data confidentiality, authentication and integrity.
VPN service includes the design, configuration and management of a firewall that provides a secure encrypted tunnel of your data transmitted over the Internet.
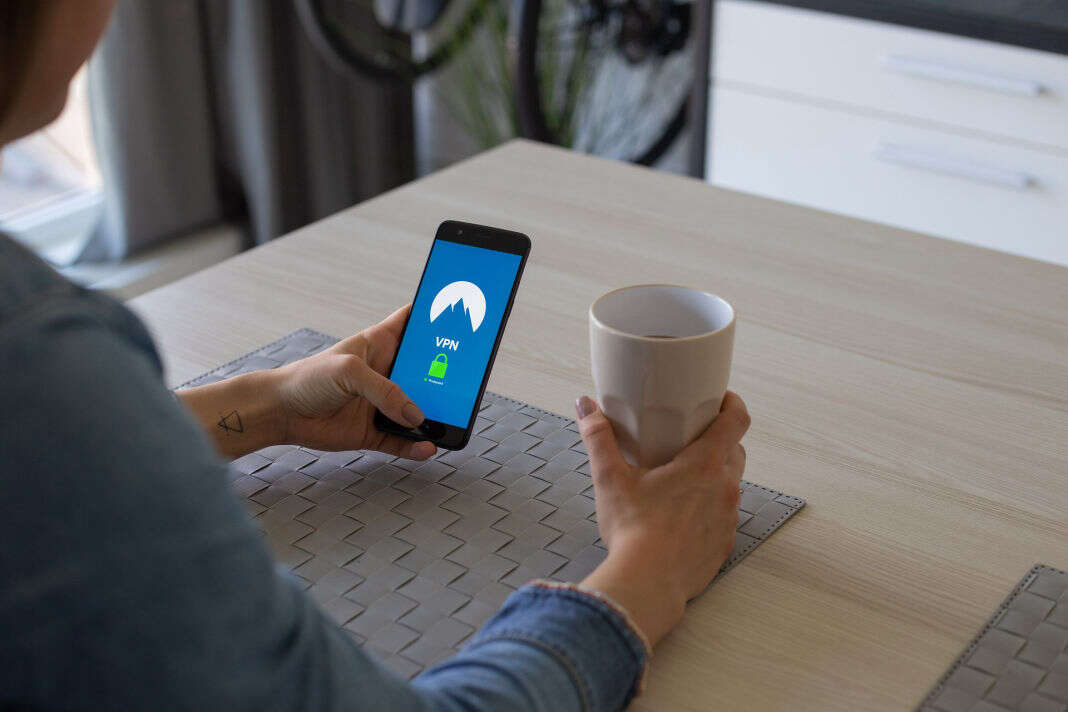
Easy, Secure Remote Networking
With more people working from home, remote-access VPNs have become an invaluable tool for many organizations, giving employees the ability to authenticate into their company’s network and browse as if they were in the office.
Remote data centers and offices need options for secure connections. VPNs are a cost-effective way to extend your network to any location where broadband connectivity is available. VPNs support remote devices and site-to-site communications with any network, data center, or other connection point.
VPN Security
In order to protect your company’s data and reputation, you need a VPN that ensures all traffic is encrypted and secured so data can’t be leaked or stolen. We deliver a powerful combination of expertise and management tools to help secure your environment and data.
• Secure access between your computer and your business’ data, even on public networks.
• Role-based access to restricted data dependent on the employee.
• Remote access to your corporate network from anywhere.
Secure access to your private network with an economical business VPN solution built to scale with your company. Saggio Technologies will set up the best VPN for your unique needs, which is essential to keep your business as safe and secure as possible in 2020.
Password resets
VPN lockout rescues
VPN Firmware upgrades
multi-factor authentication